Modern affiliate marketing — especially in competitive verticals like iGaming, finance, nutraceuticals, and insurance — is inseparable from the need to bypass sophisticated monitoring systems used by ad networks, payment gateways, and compliance departments. Public VPN services and standard proxy protocols like Shadowsocks or conventional Trojan have become ineffective: their signatures are easily identified through deep packet inspection (DPI), leading to immediate server blacklisting or account-level suppression.
VLESS with the Reality extension represents a fundamentally new stage in traffic masking technology. It allows your connection to blend completely with ordinary HTTPS traffic to trusted destinations, leaving no identifiable digital fingerprint. For US-based affiliate marketers running Google Ads, Meta, or native traffic with antidetect browsers, this is the infrastructure layer that separates clean, scalable operations from constant account losses.
Server Infrastructure Selection and Foundation Setup
The success of building a proxy that no checker can detect starts with choosing the right hosting provider and base operating system. Many cheap VPS providers have IP ranges already listed in spam databases and ad network blacklists — starting on a flagged IP means your infrastructure is compromised before you run a single campaign.
For US affiliate operations targeting domestic offers, choose VPS providers with clean residential-adjacent IP reputation: DigitalOcean, Vultr, Linode, or Hetzner US datacenters are solid starting points. If you are running GEO-specific campaigns — Texas for insurance, Florida for nutraceuticals, specific DMAs for iGaming — choose server locations as close to your target GEO as possible to keep latency low and behavioral signals authentic. For international GEOs served from US ad accounts, match the server location to the campaign target country, not to your physical location.
Operating system selection matters for stability and module support. Debian 11 or Ubuntu 22.04 LTS are the recommended choices — both have excellent kernel module support for Xray-core and are stable enough for sustained high-volume traffic operations. Avoid minimal or cloud-optimized OS variants that strip kernel modules you will need.
Before installing any core software, complete baseline server security hardening:
Select a VPS with a clean IP in your target campaign GEO — verify before committing to the server. Change the SSH port from the default 22 to a non-standard port to reduce brute-force exposure. Disable IPv6 if it is not required for your specific ad tool stack — IPv6 leaks are a common source of unintended IP exposure. Run the new server IP through Scamalytics, IP-Score, and IPQualityScore before any campaign use to confirm you are not starting with already-damaged reputation. Install monitoring tools — htop and nload — so you can track server load in real time when running high-volume traffic pours.
The most critical preparation step beyond IP checking is selecting your Reality donor domain. This is the legitimate website your VLESS server will impersonate at the TLS handshake level. The donor domain must support TLS 1.3 and HTTP/2, have high trust and domain authority, be located in the same country as your server, and have zero association with proxy or VPN topics. Ideal donor candidates for US campaigns are large regional news portals, major US retail or technology sites, or government-adjacent service domains — the point is that your traffic pattern will disappear into the enormous legitimate volume these domains generate. Never use gambling or ad-network adjacent domains as donors.
Deep Xray Configuration and VLESS with Reality Protocol Setup
Xray-core configuration is built around JSON files that describe inbound and outbound connections and the security parameters that govern server behavior under inspection. Install Xray-core using the official developer installation scripts — this guarantees no extraneous backdoors and correct binary path configuration in your system.
In the “inbounds” section you specify the VLESS protocol. VLESS differs from its predecessors by having no encryption at the protocol layer itself, which significantly reduces CPU load on both server and client. All security and masking responsibility falls entirely on the transport layer — which is where Reality enters and where the core of the masking architecture lives.
Reality replaces the standard TLS handshake with one that is cryptographically identical to a session with your chosen donor website. To an external observer — including DPI systems used by ISPs and corporate networks — your traffic is indistinguishable from a user browsing the donor domain. No proxy signature. No VPN fingerprint. Clean ISP-type connection classification in every checker that matters for affiliate work.
The critical Reality configuration parameters:
Key pair generation. Generate a Private Key and Public Key pair for Reality. The private key stays on the server. The public key is entered in the client configuration to establish trusted connection authentication.
Short ID generation. The Short ID is a unique identifier that serves as an additional authentication layer, protecting your server from unauthorized connections from random bots or active scanners. Every connection attempt without the correct Short ID is transparently forwarded to the donor domain — the server behaves exactly like the legitimate site it is impersonating, making active scanning detection essentially impossible.
Dest and serverNames parameters. The “dest” parameter points to the real IP or domain of the donor site. The “serverNames” list contains the permitted SNI values for connection. Any request arriving without the correct Short ID is redirected to the donor — to any external scanner, the IP appears to host exactly the site you are impersonating.
Technical considerations for TLS 1.3 impersonation: choose donor domains that use modern cipher suites exclusively and do not support deprecated protocol versions like TLS 1.1 or 1.0. Reality simulates modern browser requests — if the donor domain behaves differently from the traffic being imitated, this mismatch becomes a detection vector for advanced traffic analysis systems. Experienced US affiliates commonly use mirrors of major US technology companies or large media properties as donors, because the sheer volume of legitimate traffic to these destinations makes detection statistically implausible.
Client Software Selection and Optimization Across Devices
After configuring the server, you need a client that supports current Xray-core updates and allows flexible traffic routing control across your antidetect browser setup and ad account infrastructure.
Windows. v2rayN and Nekoray are the recommended clients for Windows-based affiliate operations. Both provide GUI interfaces for importing configurations via JSON or QR code and support system proxy mode. The critical configuration step is enabling TUN mode, which ensures all traffic from your antidetect browsers and ad account tools passes through the encrypted tunnel without DNS or WebRTC leaks. A single DNS or WebRTC leak during campaign launch is often enough to trigger account review.
macOS. Nekoray has macOS support. FoXray and Streisand provide clean macOS clients with routing control. Configuration follows the same TUN mode priority as Windows.
Mobile — Android and iOS. For affiliates running in-app traffic or managing accounts from mobile, v2rayNG on Android and FoXray or Streisand on iOS support VLESS Reality with per-app routing exclusions. This allows banking apps and messaging tools to run on your normal connection while ad account and tracking traffic routes through the VLESS tunnel.
Key client configuration elements for US affiliate operations:
Enable TUN mode for full traffic encapsulation at the kernel level — this prevents any application-level bypass that could leak your real IP. Configure Split Tunneling to route only ad account and tracking traffic through the tunnel, optimizing speed for non-sensitive applications. Set custom DNS inside the client — Google 8.8.8.8 or Cloudflare 1.1.1.1 — to prevent DNS queries from leaking to your local ISP. Enable the Fragment plugin in client configuration to break up the initial TLS Client Hello packet across several segments, defeating aggressive DPI filters used by enterprise networks and corporate ISPs. Update Xray core binaries in your client folder regularly to maintain support for the latest obfuscation methods.
MUX (Multiplexing). MUX allows multiple requests within a single TCP connection, which materially speeds up loading of heavy pages like Google Ads and Meta Business Manager dashboards. However, in some configurations MUX can become a detection signal for specific security systems. Test with MUX both enabled and disabled across your target platforms and measure stability and speed independently before committing to a configuration for active campaign work.
Browser Fingerprint configuration. In client settings, select browser fingerprints matching Chrome or Safari — the two highest-volume browsers — to maximize behavioral authenticity when ad network systems evaluate your connection profile.
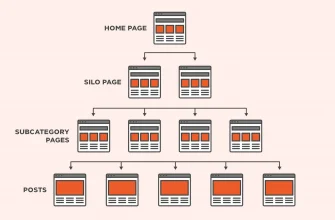
Antidetect browser integration. For affiliates running account farms through Dolphin Anty, AdsPower, or Multilogin, the optimal setup is forwarding traffic through the local HTTP or SOCKS5 port created by the v2rayN client. Each profile in the antidetect browser then uses your private VLESS server as its network connection — to the ad network, this registers as a quality residential-type connection rather than a datacenter proxy. This gives you full control over the network infrastructure of your entire account portfolio, minimizing network-pattern-based account bans at scale.
Advanced Detection Bypass and Proxy Effectiveness Verification
Setting up the proxy correctly is half the job. For US affiliate marketers, verifying that the solution actually remains invisible to all relevant checking systems is equally important — one undetected exposure point can compromise an entire account farm or media buying operation.
Primary verification checklist:
Check your IP through IP2Proxy, FraudScore, Scamalytics, and IPQualityScore — your connection should register as ISP or Business type, not Hosting, Proxy, or VPN. If any checker identifies a proxy signature, Reality masking is misconfigured or the hosting provider’s IP range is in datacenter classification databases. Check through Browserleaks and Whoer to confirm no WebRTC leak, no DNS leak, and no timezone or language mismatch between your browser profile and the IP’s registered location.
TLS fingerprint analysis. Use JA3 and JA3S fingerprint checking tools to compare your connection’s TLS fingerprint against typical browser profiles. Correctly configured Reality should produce a fingerprint completely identical to your chosen donor domain, making it impossible to distinguish your traffic from legitimate browser traffic to that domain — including under neural network traffic analysis. Any discrepancy in supported cipher suites or TLS extensions requires returning to Xray configuration and correcting the browser imitation parameters in the client settings section.
Additional verification steps for thoroughness: run Wireshark locally to capture and visually confirm absence of plaintext data in packets. Test connection speed and ping latency under load — unusual latency patterns can signal proxy presence to sophisticated detection systems. Periodically rotate Short IDs and donor domains to prevent accumulation of statistical anomalies on a single node.
Fragment mode for aggressive DPI environments. The Fragment feature breaks the initial TLS Client Hello message into multiple partial packets, disrupting protocol recognition algorithms. This is particularly relevant for US affiliates operating through corporate or carrier networks with strict DPI filtering, or for international campaigns targeting countries with active internet intervention policies. Fragment packet size and inter-packet delay parameters are tuned individually per target provider — no universal setting works for all environments.
DNS traffic security. DNS requests are a common exposure vector that affiliates overlook. In a VLESS + Reality setup, all DNS resolution must happen server-side through trusted resolvers — your local ISP should not see the domains you are actually accessing. Configure DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) within the client. This protects against both traffic analysis and DNS hijacking, which is a real operational risk when working with financial offers and ad account credentials in the same browsing session.
Operational Security Practices for US Affiliate Environments
The technical infrastructure is the foundation, but operational practices determine whether it holds up under sustained campaign operation. Several habits that matter specifically in the US affiliate context:
Never share a VLESS server across multiple distinct account identities. Each account farm or client project should have its own server — cross-contamination through shared infrastructure is a systematic account loss risk. Rotate servers on a scheduled basis — quarterly at minimum — even without any detected compromise. IP age and connection pattern history can accumulate enough statistical anomaly to become a soft detection signal over time. Keep server software updated. Xray-core releases new obfuscation improvements frequently in response to evolving DPI capabilities — running outdated versions means running against detection systems that have already catalogued your protocol version’s signature.
For Google Ads specifically: the combination of a clean VLESS Reality IP with appropriate browser fingerprinting in your antidetect browser, correct geographic timezone and language settings, and a genuine browsing history warmup period before account creation produces account profiles that perform materially better in Google’s trust evaluation than cold accounts on commercial proxy IPs. The investment in proper infrastructure setup pays back through account longevity and reduced replacement cost.
VLESS with Reality is currently the most robust private proxy architecture available for affiliate marketing operations. No public VPN product delivers equivalent undetectability — the protocol was specifically designed to make the existence of the proxy invisible at every inspection layer. For US affiliates scaling Google Ads, Meta, or native campaigns in competitive verticals, this is the infrastructure standard worth building to.
If you are scaling an iGaming or performance marketing operation and need guidance on traffic infrastructure, account management architecture, or full-cycle campaign setup — contact Denis Melnik at gamblings.tech via Telegram.